Consul API Gateway is a dedicated ingress solution for intelligently routing traffic to applications running on your HashiCorp Consul service mesh. This provides a consistent method for handling inbound requests to the service mesh from external clients.
The Consul API gateway takes all API calls from clients, then routes them to the appropriate microservice with request routing, composition, and protocol translation. This eliminates the need to install another dedicated application. Once Consul API Gateway becomes available for your services, you gain the ability to have a platform-agnostic API Gateway that is built into Consul.
Consul API Gateway is an enhancement to Ingress Controller and uses a different schema. The Consul API Gateway Controller deploys an API Gateway pod and configures the gateway, listeners, and the routes to services. If TLS is enabled on a listener, the controller will load the certificate from the Kubernetes Secrets storage. If the certificate is rotated, the Gateway Controller will automatically update the listener.
Other features of the Consul API Gateway include load balancing, modifying HTTP headers, and splitting traffic between multiple services based on weighted ratios.
In this tutorial, you will:
- Create a local Kubernetes cluster using Kind
- Install Consul using Helm or Consul K8s-CLI
- Deploy example applications HashiCups and Echo Server
- Deploy Consul API Gateway
- Explore Ingress into the service mesh with HashiCups
- Explore Load Balancing with Echo Server
»Prerequisites
»Clone GitHub repository
Clone the GitHub repository containing the configuration files and resources.
- HTTPS
- SSH
Change into the directory with the newly cloned repository.
Check out the v0.0.12 tag of the repository.
Change into the directory that contains the complete configuration files for this tutorial.
»Create a local cluster
Start Kind with the --config flag specifying the cluster.yaml configuration file.
The output will be similar to the following.
»Create the Consul API Gateway Controller CRDs
Create the custom resource definitions (CRD) for the API Gateway Controller.
»Install Consul with the official Helm chart
Add the HashiCorp Helm Chart repository:
You can now deploy a complete Consul datacenter in your Kubernetes cluster using the official Consul Helm chart or the Consul K8S CLI. The chart comes with reasonable defaults, however, you will utilize a few custom values with the config.yaml file to help things go more smoothly with kind and enable useful features.
Note: You can review the official Helm chart values to learn more about the default settings.
Security Warning: This tutorial is not for production use. By default, the chart will install an insecure configuration of Consul. Refer to the Secure Consul and Registered Services on Kubernetes tutorial to learn how you can secure Consul on Kubernetes in production. Additionally, it is highly recommended you use a properly secured Kubernetes cluster or make sure that you understand and enable the recommended security features.
»Create environment
»Create the example application pods
Deploy the Hashicups and Echo applications:
Check the pods to make sure they are all up and running:
»Inspect the API Gateway configuration file
The API Gateway Controller consists of multiple components that facilitate ingress into your Consul service mesh.
Inspect the api-gateway/api-gw/consul-api-gateway.yaml file contents in your project directory:
This configuration file uses the following components:
Gateway- This object is the main infrastructure resource that links all other related configuration information together. The spec itself defines listener and address details. To see more details about this type, see the Kubernetes Gateway documentationGatewayClass- This object (deployed and configured by the Helm chart) describes a class of Gateways available to the user for creating Gateway resources. To see more details about this type, see the Kubernetes GatewayClass documentationGatewayClassConfig- This object (deployed and configured by the Helm chart) describes additional Consul API Gateway related configuration parameters for theGatewayClass.
Note: Feel free to explore additional configuration details in the Consul API Gateway documentation.
»Inspect the Routes file
Routes tell your Consul API Controller how to handle traffic into your service mesh.
Inspect the api-gateway/api-gw/routes.yaml file contents in your project directory:
This configuration file uses the following components:
HTTPRoute- This object specifies routing behavior of HTTP requests from a Gateway listener to a Service. Rules and matches within this type define conditions used for matching an HTTP request. To see more details about this type, see the Kubernetes HTTPRoute documentation.example-route-1- ThisHTTPRoutedefines the load balancer settings for theecho-1andecho-2services.
example-route-2- ThisHTTPRoutedefines the ingress settings for thefrontendservice.
Note: Feel free to check out the Kubernetes HTTPRoute documentation for configuration options and details.
»Create the Consul API Gateway
Deploy the API Gateway.
Deploy the associated HTTP Routes once the API gateway reaches a ready state.
Run kubectl get pods to verify all pods have been properly created
in your cluster. Your environment should look similar to the list below:
»Perform testing procedures
»Explore the Consul UI
Run kubectl get pods to verify all pods have been properly created
in your cluster. Your environment should look similar to the list below:
Expose the Consul UI with kubectl port-forward using the consul-ui service name as the target.
Check out the Consul UI at https://localhost:6443. Since this environment uses a self-signed TLS certificate for it's resources, click to proceed through the certificate warnings.
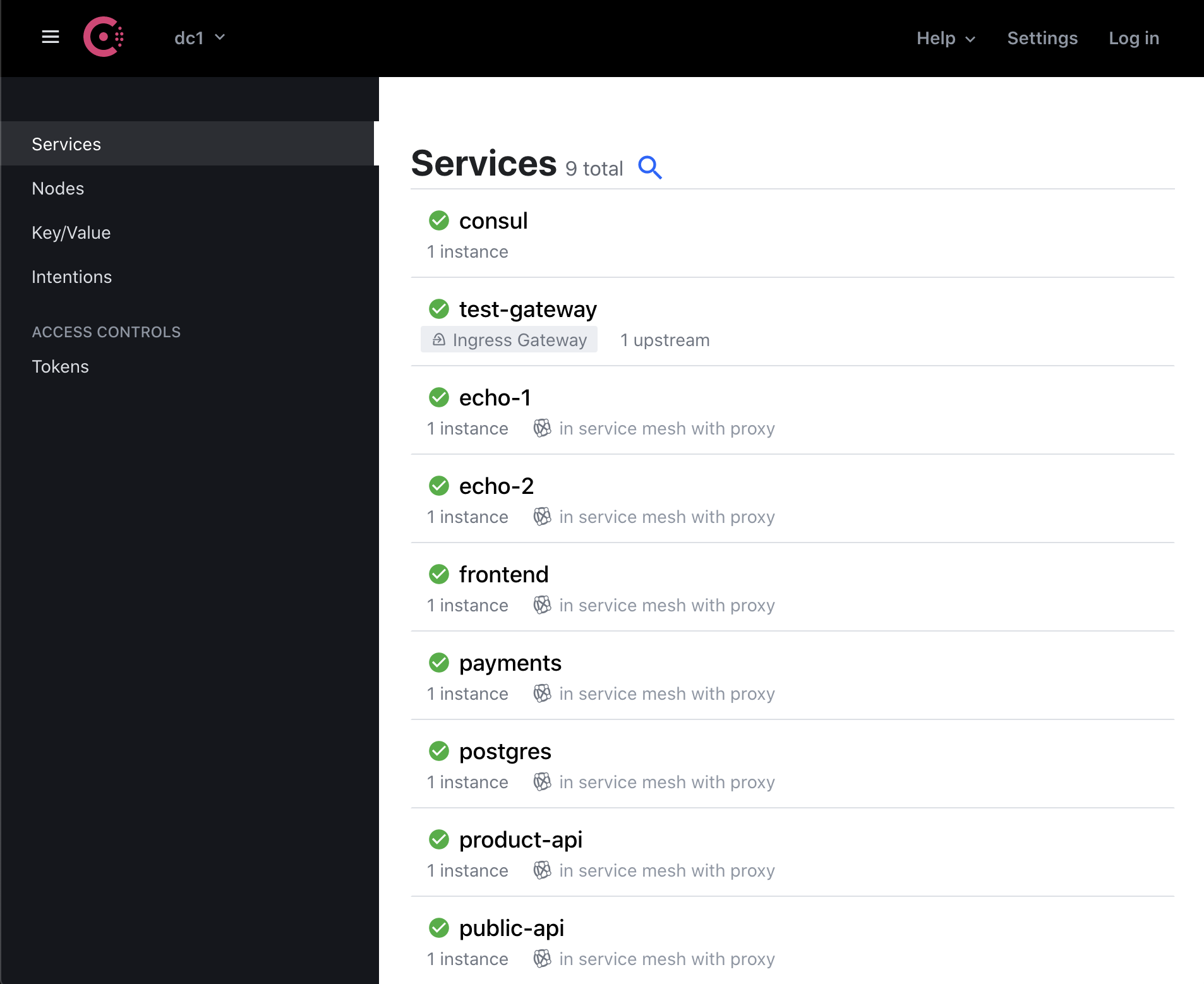
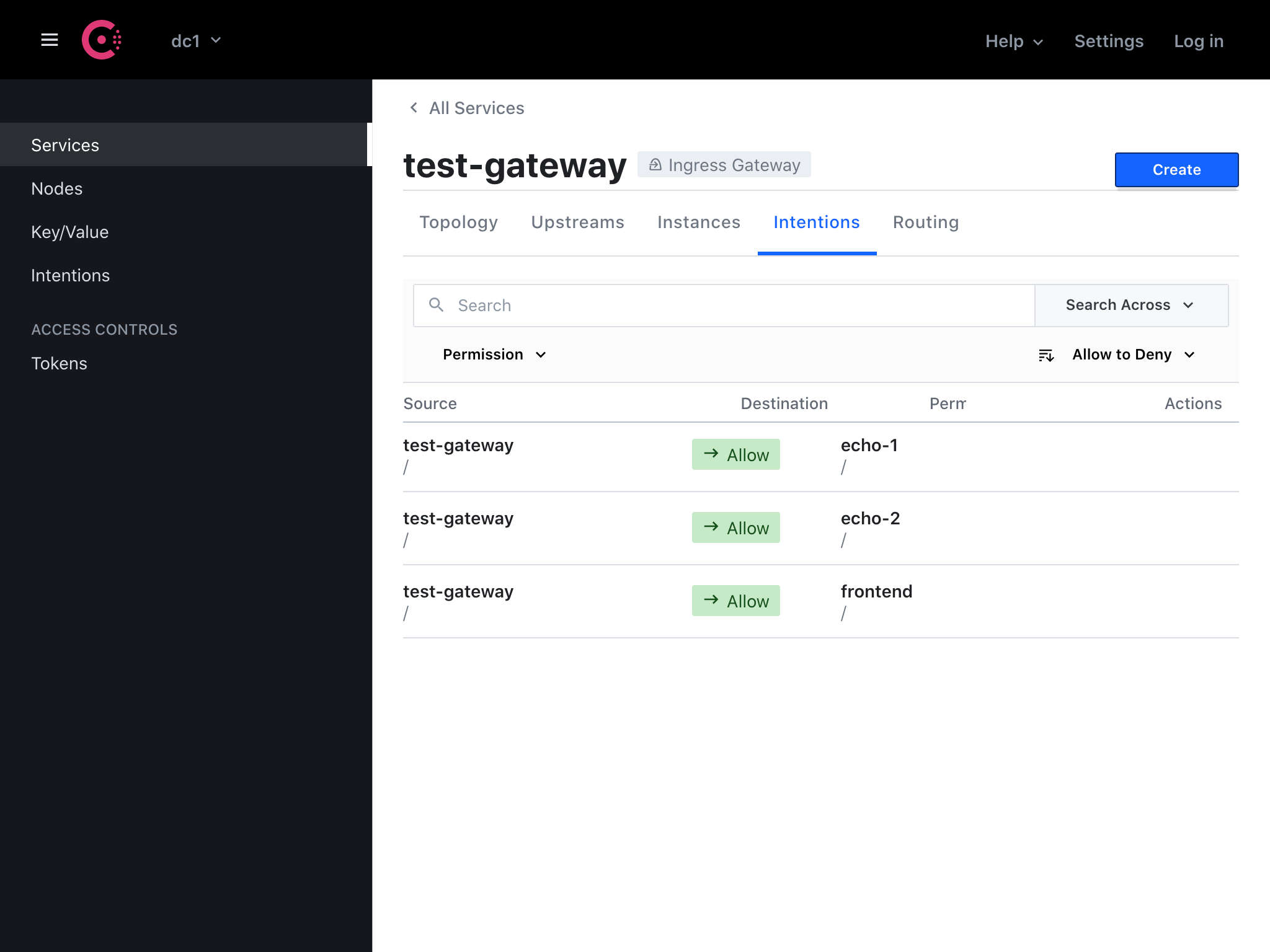
When the API Gateway has been successfully deployed, the Hashicups and Echo services will appear as intentions here: https://localhost:6443/ui/dc1/services/test-gateway/intentions
»Explore the sample applications
The diagram below shows the structure of the Kubernetes cluster you have created. This includes the API Gateway Controller, the service mesh layer, and various pods.
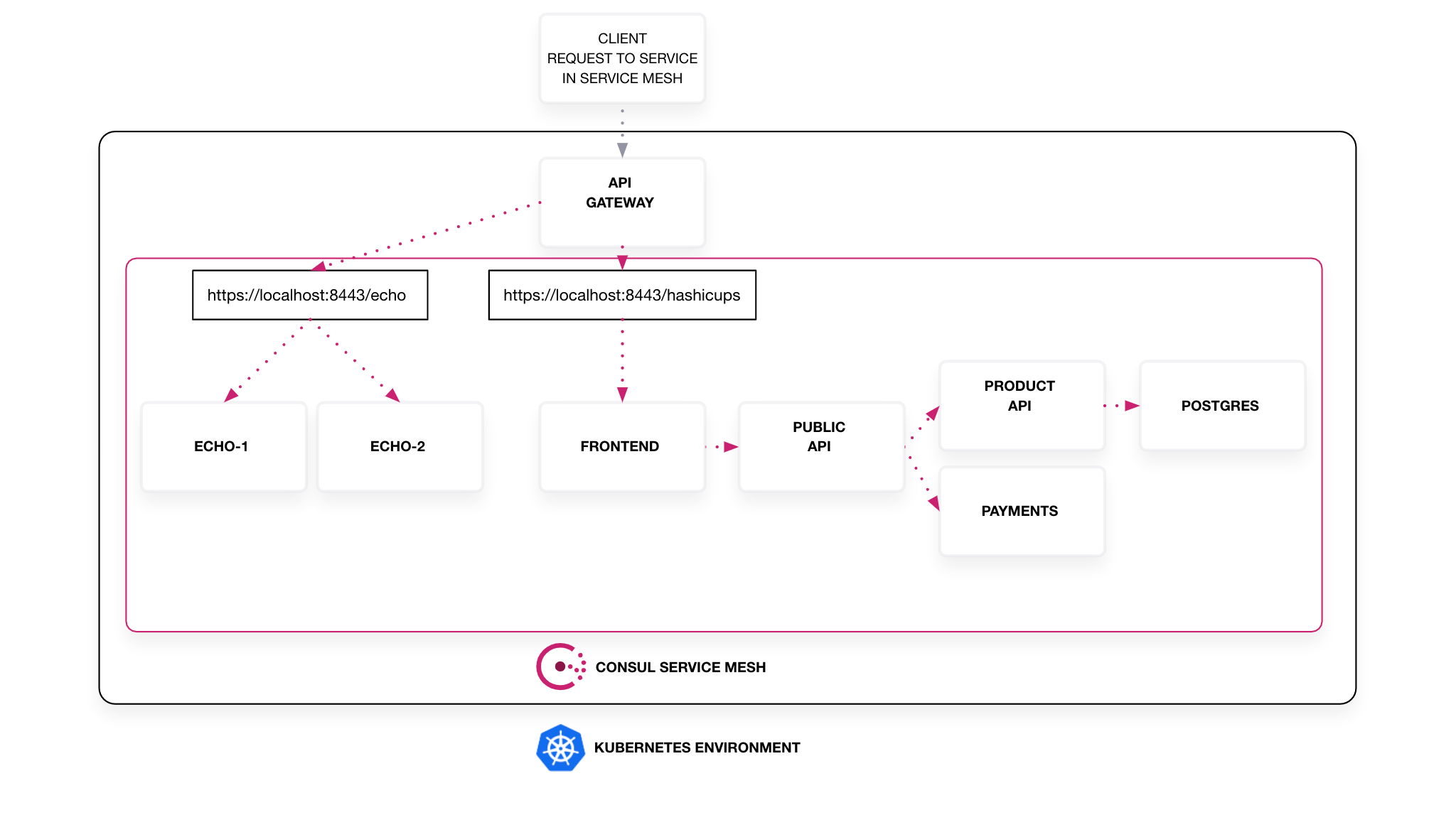
The Consul API Gateway can be configured to handle ingress for multiple services using a variety of methods.
»Use Case 1: Ingress
The Consul API Gateway can easily be configured for ingress into your service mesh applications.
In this tutorial, the Consul API Gateway provides ingress to the Hashicups service. You can access the Hashicups frontend UI through the API Gateway at https://localhost:8443/hashicups. The Hashicups application is a collection of pods that together form a microservice application.
To review, this HTTPRoute code snippet from the api-gateway/api-gw/routes.yaml file is what enables the single-service ingress behavior to the frontend service.
»Use Case 2: Load Balancing
The Consul API Gateway can also be used to load balance between multiple services within your service mesh.
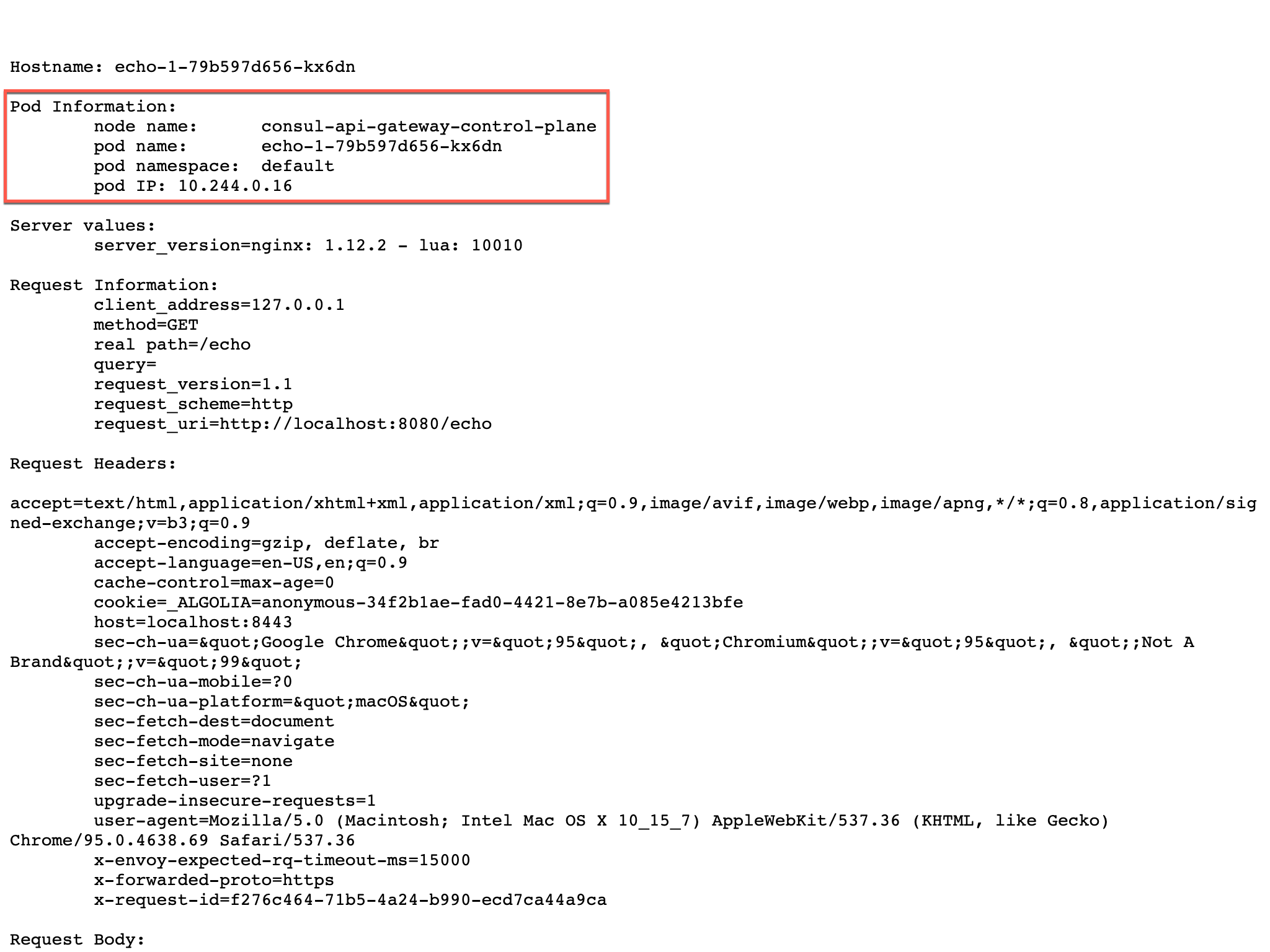
In this tutorial, the Consul API Gateway load balances between two separate Echo Server services. Check out the Echo Server frontend UI at https://localhost:8443/echo to see that the API Gateway is successfully routing traffic into the service mesh. Reload the page several times to notice how the load balancer alternates requests between the two different pods.
To review, this HTTPRoute code snippet from the api-gateway/api-gw/routes.yaml file is what enables the load balancing behavior between the two echo services.
Note: For more information on accessing service mesh services via the Consul API Gateway, visit the Consul API Gateway documentation page.
»Clean up environment
Clean up the environment you just created:
»Next Steps
In this tutorial, you used the Consul API gateway as an ingress solution for routing traffic to the applications running on your HashiCorp Consul service mesh. The environment you created in this tutorial highlighted the benefits of using the API Gateway for secure traffic ingress to multiple services as well as load-balancing.
Utilizing Consul API Gateway as your dedicated ingress solution eliminates the need to install and manage additional applications for handling traffic ingress. Once Consul API Gateway becomes available for your services, you gain the ability to have a platform-agnostic API Gateway that is built into Consul.
Feel free to explore these tutorials and collections to learn more about Consul service mesh, microservices, and Kubernetes security.







